Goodbye Air Gaps, Hello Improved ICS Security
The start of a new year is often the time we make decisions to do things differently than in the past. We'd like to suggest one of the 2016 decisions you make is to toss out invalid ICS security assumptions and hone in on meaningful improvement for your cybersecurity defenses. To illustrate, we'll review an “old” security approach–air gaps. Those at the forefront of security may have dismissed air gap approaches, but many engineers in the field still consider air gaps valid defense measures.
Let's take a look at air gaps as security control and consider why for those concerned with automation network reliability and availability, it's time to forget them as a method of defense.
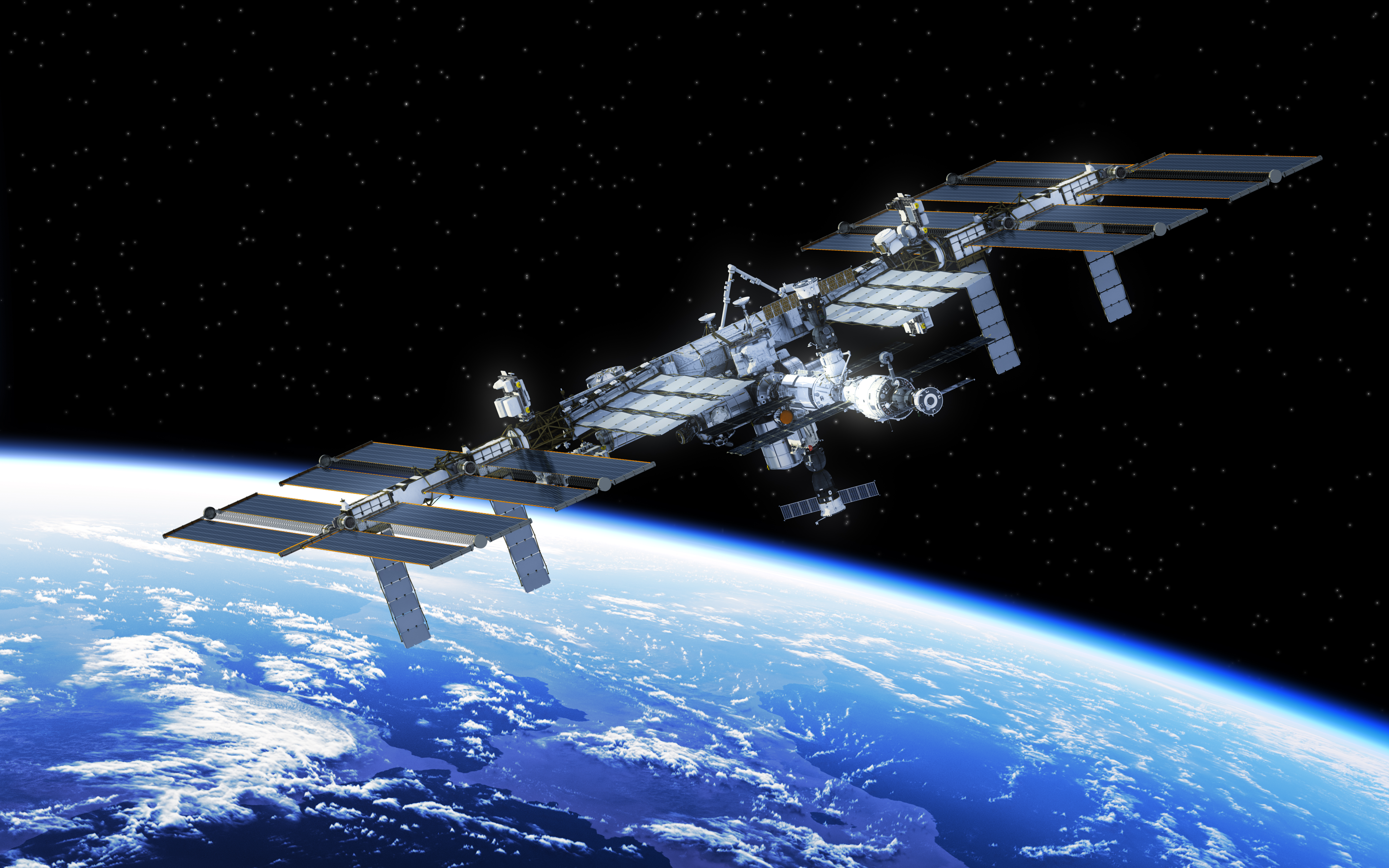
Proving there are multiple pathways to control systems, in 2013 the International Space Station was infected by a virus introduced via a USB storage device.
ICS Security & the Air Gap Myth
An air gap is a physical gap between the control network and other networks such as business networks or the Internet. The concept is that a physical gap can stop hackers and their tools, such as malware or unauthorized remote access software.
Before LANs and the internet came along, functional air gaps did exist–see the black and white photo shown on this page for an example.
Modern control networks, however, require a steady flow of electronic information with both enterprise and third party networks that can open up vulnerabilities or exploitable weaknesses. If you think you have an isolated system, read this conversation between a control engineer and SCADA security expert Eric Byres.
Therefore, a common prescription from vendors as recently as a few years ago included mitigation steps including, “It's important to isolate the automation network from all other networks using an air gap.”
In today’s competitive world, the demand for real-time data and continuous improvement has meant that links between control networks and business networks are inevitable:
"In our experience in conducting hundreds of vulnerability assessments in the private sector, in no case have we ever found the operations network, the SCADA system or energy management system separated from the enterprise network. On average, we see 11 direct connections between those networks. In some extreme cases, we have identified up to 250 connections between the actual producing network and the enterprise network.” Sean McGurk, former Director, National Cybersecurity & Communications Integration Center (NCCIC), Department of Homeland Security.
Whether it's production data, remote support, supply chain integration, engineering enhancements or even simple PDF reader updates for manual reading, connecting with other networks is a defacto requirement.
Multiple Pathways to Control Systems
Perhaps you accept our argument that automation networks are connected to enterprise networks. But you still believe it’s possible to isolate control networks from third party systems using a “no-internet” air gap.
A major change in thinking in this regard occurred after Stuxnet was discovered and its infection methods analyzed. Our white paper How Stuxnet Spreads–A Study of Infection Paths in Best Practice Systems showed how a high security “air gapped” nuclear enrichment plant was breached using an infected USB device. Among its conclusions:
- A modern ICS or SCADA system is highly complex & interconnected, resulting in multiple potential pathways from the outside world to the process controllers.
- Assuming an air gap between ICS & corporate networks is unrealistic, as information exchanges are essential for process and business operations to function effectively.
- All mechanisms for transfer of electronic information (in any form) to or from an ICS must to be evaluated for security risk. Focusing security efforts on only a few obvious pathways (such as USB storage drives or the Enterprise/ICS firewall) is a flawed defense.
Another example that disproves the notion that air gaps are an effective defense is the Dragonfly malware campaign. Discovered in 2014, it targeted the pharmaceutical industry. One way it obtained access to ICS networks was via malicious payloads inserted into legitimate software updates provided on vendor websites.
Industry expert Joel Langill states on this cyberattack:
"Equipment like PLCs and SCADA RTUs that are typically disconnected from the internet are often believed to be immune from attacks using more common social engineering vectors. This attack showed the potential of using tactics involving trusted supply chain vendors to deliver malicious payloads directly to difficult-to-reach endpoints, such as ICS equipment."
In his presentation “Why Control System Cybersecurity Sucks” Dr. Stefan Lüders, Computer Security Officer, CERN, declares “the air gap is a myth”.
Example of Air Gap Myth-Busting Cyberattack–Black Energy
To further kill the myth of air gaps as a valid security measure, let’s look at the milestone cyberattack that occurred recently, just before Christmas 2015 in the Ukraine. Here are the key details:
- A Western Ukrainian power company reported a power outage on Dec. 23, 2015
- The investigation into the incident revealed that malware called “BlackEnergy” or “DarkEnergy” disrupted systems which led to the outage
- Infection occurred when someone in the target organization received a “spear phishing” email with a malicious attachment & clicked on it
- The event is notable and important because it is the first known cyberattack to cause an electricity blackout.
For more information, see this BlackEnergy Malware article drafted by our cybersecurity business unit, Tripwire.
This type of technique, known as social engineering, is another pathway into control networks. While a simpler infection technique than those used for Stuxnet and Dragonfly, its impact was very significant.
How well are the employees in your organization trained to identify and disregard dubious emails?
Most Security Incidents Occur Inside the Control Network
Besides the fact there are multiple routes into the control system, another major flaw with the air gap approach is that most industrial cyber security incidents originate INSIDE the control network. Our experience with clients around the world indicates that causes such as these are common:
- Misconfigured firewalls or switches
- Unpatched computers or systems
- Poorly segmented networks
- Device or software error
- Accidental introductions of malware
Industry data in this area is scarce, but RISI figures from 2011 also indicate that events within the control network account for the majority of control network cyber incidents. Even if air gaps did work, they wouldn't protect your ICS from downtime and performance risk from the majority of cyber occurrences.
Instead of relying on the air-gap crutch, let's take a hard look at the cyber risks facing your organization and the security controls you have in place to deal with them. An overview of the most important ICS security threats and controls is provided in this article.
Time to Discard Air Gaps and Act on Cybersecurity
We can’t stress this enough–90% of industrial cybersecurity is not about blocking hackers–it’s about ensuring high availability and reliability through hardened, resilient systems.
![System.String[]](https://assets.belden.com/transform/7d9664bf-965d-4965-a32d-382a9829c061/Author-Belden-Logo-sm-blue-2020-10?io=transform:fill,width:300,height:300)