SCADA Security: Securing DNP3 Communications with Defense in Depth
Two things that make ICS cybersecurity different from IT security are the use of industrial-specific protocols like DNP3 and the common usage of endpoints like PLCs, IEDs and RTUs that are 15+ years old. Both of these factors are significant in industries that depend on WAN communication networks, such as power, water/wastewater, transportation plus oil and gas systems.
Recently two SCADA security experts, Erik Schweigert of Belden and Joel Langill of SCADAhacker.com, gave a webinar that described the challenges of securing systems like power grids. In it they explained why field firewalls and Deep Packet Inspection play important roles in cyber resiliency for many types of critical infrastructure.
Top 10 Things to learn about SCADA Security
10. Unique Advantages of DNP3 Communications
DNP3 (Distributed Network Protocol) and its European counterpart IEC 60870-5-104 are very good at communicating over low bandwidth Wide Area Networks (WANs). This makes DNP3 ideal for power grids and other SCADA systems like oil and gas pipeline management systems. [Webinar 5:10-7:02]
9. Why Power Grids Using DNP3 are Particularly Susceptible to Remote Attacks
While DNP3 is a master/slave protocol like Modbus, DNP3 supports unsolicited messages like report-by-exception messages from slaves to master. This exposes power grids to large remote attack surfaces. For example, in the Marochy-Shire sewage system attack, false information from a field station was sent to the command center and the outcome was one million liters of spilled sewage. [7:02 – 11:05]
8. Embedded Devices Can’t be Protected with Host-based Solutions
Joel does a great job of explaining why, for industrial security, host-based endpoint protection measures are insufficient.
There are very few security controls available for installation on devices like PLCs and IEDs. Thus, an important way to protect them is to use network entry point security controls. This is a foundational concept for the Zones and Conduits discussion coming up later. [11:10-13:10]
7. ICS Security is Not All about Hackers; it is Essential for Reliability Too
Learn how 3 cyber incidents, unrelated to malware, brought down energy systems and automotive plants, causing downtime with high financial costs. [13:11-14:55]
15-25 year old control equipment, designed before the Internet, is still in active use in many industrial systems. Don’t miss Joel’s interesting comments on this, highlighting how these legacy devices need to be protected from network traffic that they can’t tolerate. [14:56-18:06]
6. Excellent Animations Showing How 2 Types of Cyber Threats Impact Industrial Networks
Erik does an excellent job using a network diagram with animations to show how malware can bypass the plant boundary firewall to get to the control system. He also shows how a network device failure can take down a group of PLCs. His visuals are great for understanding the unique challenges of ICS security. [18:06-21:45]
5. How to Segment an Industrial Network for IEC 62443 Zones and Conduits
The IEC 62443 Zones and Conduits model is a key part of Defense in Depth for ICS systems. See how Erik applies it to his example control network.
Industrial firewalls used at the field level are conduit-based security controls that protect automation systems from malware and accidental internal network incidents such as device failures or human error.
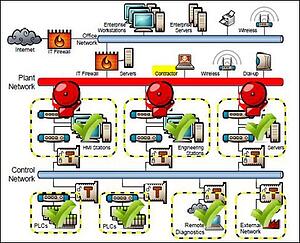
Joel makes the interesting point that Zones and Concepts is a hard concept for IT to “get” as there is no standard enterprise equivalent for it. He also explains how it can be used to protect PCs and embedded devices using Windows XP [21:50-28:28]
The impact of malware introduced on a contractor laptop is contained by conduit-based security controls (Tofino Xenon industrial firewalls) that protect groups (zones) of similar equipment.
4. What Deep Packet Inspection (DPI) Is and Why Protocol-Specific DPI is Important for ICS Security
Who better to describe Deep Packet Inspection than the developer who has implemented it in Tofino Security products? Erik has a nice way of explaining it and he also differentiates protocol-specific DPI from signature-based DPI. [30:36-36:24 and 38:08-42:09]
Erik and Joel have a good discussion on the importance of taking into account real-world applications when implementing protocol-based DPI in a firewall. (In this respect Belden thanks Adam Crain, “Mr. DNP3”, for his contribution to the development of the Tofino DNP3 Enforcer.) [36:25-45:30]
3. Why ICS Security Solutions Need to be Easy for Engineers to Implement
Implementing DPI has to be easy for PLC programmers to do; otherwise it either won’t be done or will be done poorly, jeopardizing security. [45:30-47:24]
2. The Advantages of the Tofino Security Appliance for Industrial Security
This is the product discussion – focusing on the key ways industrial firewalls are different from IT firewalls. [47:24-50:00 plus the Q&A 50:05-53:18]
1. Unique Opportunity to Learn from Two ICS security Experts
There aren’t many true ICS security experts out there. This webinar is given by two of them. Don’t miss the chance to learn their unique insights from years in this field!
(Erik Schweigert is a cyber security researcher and engineer who has developed pioneering Deep Packet Inspection technology for ICS systems. Joel Langill has more than 30 years' of experience securing global industrial control systems and is the founder of Scadahacker.com.)
![System.String[]](https://assets.belden.com/transform/7d9664bf-965d-4965-a32d-382a9829c061/Author-Belden-Logo-sm-blue-2020-10?io=transform:fill,width:300,height:300)