ICS Security for Industrial Networks (Part 1)
It’s not a surprise that ensuring the reliability and availability of control systems is a leading priority for securing industrial automation systems as confirmed in the SANS 2016 State of ICS Security Survey. Other top reasons for improving security include lowering risk, ensuring employee safety, meeting regulatory compliance and preventing system damage and data loss.
Combine these concerns with the fact that 67% of SANS survey respondents perceived a severe or high level of threats to control systems (up from 43% in 2015) and it’s clear that effective industrial security programs are needed. The next challenge is, how?
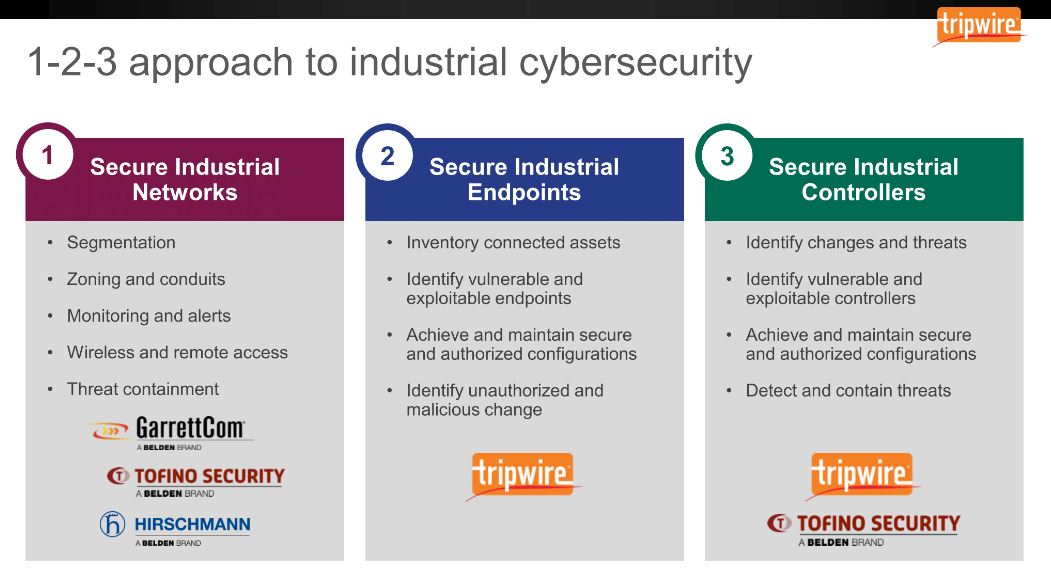
To address the 'how', we introduced a 1-2-3 approach to industrial cybersecurity focused on dividing security measures into three areas:
- Securing the network
- Securing the endpoints
- Securing the controllers
Similar to government standards such as NIST, you don’t have to approach this in a 1-2-3 order. Instead, start your focus in the area that aligns with the highest risk to your systems and fits with where your organization is in its security journey.
This article will start with the 'Why' and 'How' of securing industrial networks.
The Belden 1-2-3 approach to industrial cybersecurity provides a model that organizations are finding helpful in terms of prioritizing and organizing their security programs.
Industrial Security Starts with Good Network Design
Top industrial security threats that worry plant engineers and IT professionals include attacks from external sources such as hackers, hacktivists and nation states as well as unintentional incidents that disrupt systems. Both are likely to involve network communications. Examples include:
- Penetrating a network boundary & using a network or industrial protocol to transmit malware to an endpoint
- Connecting a contractor laptop or employee mobile device to the industrial network & introducing malware that travels to other plant devices
- Incorrect device configuration that broadcasts a traffic storm disrupting legacy industrial devices
This is the reason that the number one best practice recommended by standards organizations, ICS-CERT, SCADA security experts and Belden is to make sure you have a good network design with well-secured boundaries.
The recently published ICS-CERT 2015 ICS Assessment Summary Report, for example, calls out weak boundaries between ICS and enterprise systems as a top vulnerability found in their deep dive assessments of critical infrastructure facilities.
Furthermore, even with a good enterprise-plant boundary, the days of counting only on perimeter defense are long gone. As examples 2 and 3 above show, there are many pathways into control systems. Your challenge is to contain communications in appropriate areas or sub-systems and prevent threats from migrating to other areas. That’s why it’s also necessary to implement many inside-the-plant-network security zones.
Segmenting Networks for ICS Security
One of the most important ways of segmenting industrial networks for security purposes is to implement the ISA IEC 62443 standard, section -3-2 , that calls for the use of security zones separated by conduits.
A security zone is a group of assets that share common security requirements (e.g., a supervisory zone and a controller zone). Each zone has a defined border that can be logical or physical, delineating which assets are included and which are not.
Communications between zones must be via a defined conduit. A conduit is any pathway of communication that enters or exits a security zone. The conduits are the perfect “choke points” for implementing security measures, such as industrial firewalls, to ensure that only the traffic needed by plant systems is allowed to pass.
Conduits compensate for the fact that the devices they protect have insufficient built-in security. In addition, focusing on conduit mitigation is typically far more cost effective and realistic than having to upgrade every device or computer in a zone to meet security requirements.
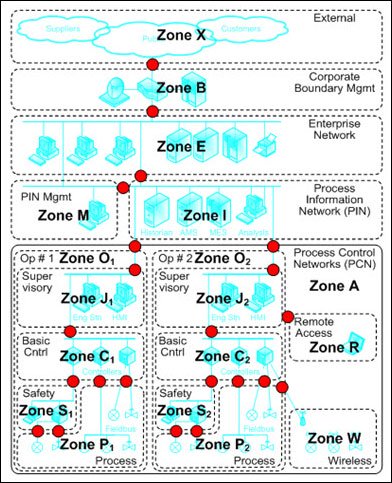
This simplified diagram of an oil refinery shows how its systems were grouped into zones. The red dots represent the conduits between the zones. NOTE: The safety system is in its own zone, highlighting its importance.
Other than the zones and conduit model, segmenting networks can be done by implementing subnets, VLANS and VPNs.
Securing Industrial Wireless Applications
Industrial wireless applications are being used more and more by leading manufacturers and operators to improve availability and reduce costs. And, today’s best practices, technologies and products make it straightforward to implement them securely. Use the tips listed below for securing the plant network when wireless is involved.
|
BEST PRACTICE TIPS |
DETAIL |
| Segmentation |
|
| Monitoring |
|
| Technologies & Standards |
|
| Products |
|
Secure Remote Access to ICS
Remote access to industrial networks is a key enabler of fast troubleshooting and problem resolution, as well as a travel and time cost saver. It is also increasing in importance as plant systems incorporate more devices with intelligence as part of the Industrial Internet of Things (IIoT) trend, thus requiring support from more organizations.
The challenge is how to provide remote access in a way that is secure yet not complex. The traditional solution has been to use VPNs, but they can be difficult to use, create high administrative overhead and do not guarantee that only legitimate data is transferred.
New secure remote access solutions have recently been introduced that provide industrial engineers with tools that are easy to implement, don’t require IT resources and are highly secure. These industrial-focused approaches will increase in capability over time and make it easier to leverage worldwide engineering and technical expertise in cost effective ways.
Monitoring ICS Networks
Monitoring the security status of a network is common practice for IT networks but less common in the OT environment. It is increasing in use, however, and one way of doing it is to connect virtual-machine-based security software to the switch or router that connects the IT/plant DMZ boundary.
The VM machine passively (or non-invasively) collects packet flows, without impacting network operations, and analyzes them for anomalous or undesirable connectivity to the Internet or business network. It can also analyze log sources and apply intelligence and rules to identify malicious / anomalous activity.
Another facet to consider is the value of monitoring industrial network infrastructure equipment such as routers, switches, gateways etc. These systems connect the segments and can be compromised. They need to be assessed, a baseline taken and a monitoring effort applied. Some organizations have their IT teams managing the security and configuration of these devices.
Securing Industrial Networks is One Dimension of Defense in Depth
Following best practices and using the technologies outlined above will go a long way to securing your communications infrastructure. Securing industrial operations environments need to be considered holistically, however. This involves also securing endpoints and control systems themselves.