ICS Security Tips for Public Transportation Systems
The answer I believe, is that until now, the transportation industry hasn't been under pressure to increase capacity while also improving efficiencies. Efficiency in this case means improving financial returns and consuming fewer natural resources.
Let’s look at how in this challenging environment, passenger rail and public transportation systems can improve their Industrial Control Systems (ICS) security.
Adoption of Ethernet Networks Increases Cyber Threats
To realize improvements in performance and capacity, rail operators are leveraging technology advancements while also seeking to reduce capital expenditures. This inevitably means a shift from traditional legacy systems using stand-alone bespoke equipment to a greater use of standardized technologies, protocols and operating systems (e.g., Ethernet).
These newer technologies typically have open interfaces and standardized protocols. Consequently, as they're designed into control and communication systems at an increasing rate, the risk to transportation systems from cyber attacks also increases.
In addition, to achieve superior value and an increased level of customer service the inter-connectivity between what have previously been stand-alone systems, is greater than it has ever been before. An example is connecting train control systems with seismic or tunnel drainage monitors for enhanced safety and reliability. This inter-connectivity, sometimes using leased lines of communication infrastructure, also creates a new and real risk when it comes to cybersecurity.
Cyber Risk Extends Beyond Safety Risks
But does cybersecurity really matter, given the fail-safe methodologies used within the transportation industry? It is true that a safety-focused culture, particularly within the rail sector, mitigates some of the immediate risk, but not the consequential risks.
By consequential risks I mean that the ongoing operation of a compromised transport system may be degraded rather than actually halted; late running trains or some ticket barriers not working for example. In addition, as operational systems become more complex, reliably achieving fail-safe conditions is more challenging, especially when subjected to a deliberate cyber attack.
It is also important to note that the cyber risks are not limited to safety. Cybersecurity has the potential to affect the whole supply chain. Failures in the supply chain, especially those that persist for a few days, will quickly have a direct operational impact. For example, spare parts may not be delivered to a maintenance depot, resulting in trains being out of service and a degraded operational service.
There are also reputation and commercial risks, especially when attacks directly affect passengers or passenger services. Finally, the media interest in cybersecurity has the potential to give wide coverage to even minor incidents; any response to transportation related cyber attacks will be in the public domain and will have a high impact on passenger trust in the system.
ICS Security Standards for Public Transportation Systems
Increased cyber risk is the reason groups such as those below have published cybersecurity recommendations for rail operators:
- American Public Transportation Association
- US Computer Emergency Readiness (cyber Infrastructure)
- European Union Agency for Network & Information Security
Thanks to the recommendations of these groups plus the overall ICS cybersecurity standards developed by ISA and IEC (ISA IEC 62443) there are a lot of resources available to turn to for guidance. But it doesn’t have to be overwhelming; here are some helpful principles to guide you.
Begin with a Risk Assessment
Taking the first step in a new area is always the hardest, but take heart; guidance is available. The best practices incorporated into the industry and government recommendations mentioned above are available to guide you.
The first step is to conduct a risk assessment; you need to understand what your network looks like and where the critical assets are. Then think about your risk tolerance for the different assets. It will be different, for example, for signaling systems versus passenger Wi-Fi services.
This might sound like a big project, or a costly consulting engagement. However, it is possible to do it internally and at no cost. While this may not be for everyone, it could be a viable option if a third-party assessment is not in your budget right now. It is also better than doing nothing about improving the security of your ICS network.
A risk assessment is important and is not a one-time event. Good security requires monitoring, evaluating and improving your plans regularly in order to ensure current measures are working effectively. This will also help you recognize new or developing risks to the network.
Develop a Defense-in-Depth Strategy
After completing the risk assessment, the next step is to create a plan to secure your network. Again, using the collected knowledge of the experts in this area, the approach you want to take is called Defense in Depth (DiD), which basically means multiple layers of defense distributed throughout the network.
A well considered DiD strategy includes:
- Multiple defense layers vs relying on a single point of security
- Differentiated defense layers to ensure an attacker can’t access subsequent layers after getting past the first
- Context & threat-specific defense layers, meaning each layer is optimized to manage a specific threat class
- Defense zones where devices with similar security requirements are secured by a conduit (as per ISA IEC 62443 standard)
If your network is protected by a DiD strategy, the impact of an accidental security incident or a malicious attack will be limited to the zone where the problem began. You want to set up your systems so that the right people or teams receive an alarm and start working on incidents in a timely fashion.
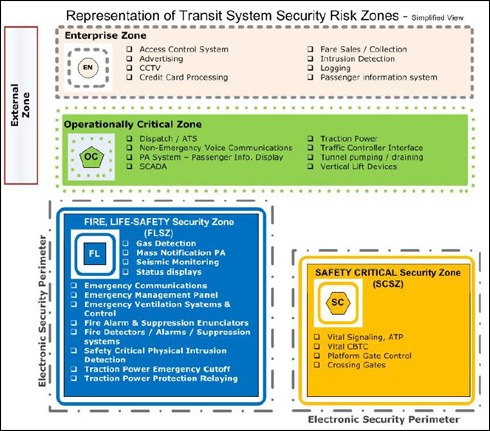
This diagram groups together devices and systems with similar security requirements. The next step, as per the ISA 62443 standard, would be to specify conduits, such as industrial firewalls, to control communications between the zones. (Source: APTA Part II)
Tip No. 3: Protect Critical Assets First
Lastly, you must prioritize the critical assets. These are the systems that would cause a complete disaster for your network if they were shut down (either unintentionally or maliciously).
For a passenger rail system, typical examples would be the remote terminal units (RTU) in signaling control systems or the network infrastructure running a Communications-Based Train Control (CBTC) system. Aggressively protect these assets and the chance of a truly serious cyber incident is greatly reduced.
Get Started on Cybersecurity for Public Transportation Systems
Don’t let these challenges stop you from effectively protecting your transportation systems.
- Efficiency challenges of the day
- Complications brought on by increased connectivity
- High cost of formal risk assessments
By taking the right steps to understand your risks, choosing a layered approach, and prioritizing your most important assets, you can successfully implement good cyber defenses.
What are the challenges you face in implementing cybersecurity measures? Do you have any tips to pass onto others? We look forward to hearing from you.