Industrial Automation
How to Manage Users and Devices with Network Access Control
08.22.2022
Network security isn’t a fixed state you can achieve once and then simply work to maintain over time. There are many variables that affect how network security is managed.
For example, in the race between IT experts and IT cybercriminals, network security is always adapting to changing threat situations.
As processes become more integrated, workflows become more complex and global, and networks experience increasingly dynamic changes due to expansion and technical development, cybercriminals change their approaches—which means that IT experts must deploy new security tactics to defend their networks against these attacks.
Further transforming network security are new ways of working. Today, security needs to protect and support digitization and automation, hybrid and remote work, IIoT and the cloud.
How can IT experts keep up with constantly changing security requirements?

It Starts with Network Access Control
A network access control (NAC) solution boosts network security, visibility and management by preventing unauthorized users and devices from accessing your private network.A network access control solution is easy to install, too. Within a few hours, an NAC solution can be up and running to graphically map your network topology in real time.
It offers an up-to-date overview of all devices on the network so you can see everything as it happens—and receive alerts when devices attempt to connect so you can deny or grant access. In addition to mapping the network itself, a network access control solution also maps connections between endpoints (PCs, printers and all IT and OT devices, for example).
This offers several benefits:
- Quickly locate network misconfigurations
- Uncover unknown devices on your network
- Pinpoint network weaknesses and vulnerabilities
- Efficiently identify and monitor endpoints to prevent unauthorized access
Combining a network access control solution with other identity sources—such as configuration management databases (CMDBs), asset management, AD/LDAP and mobile device management (MDM)—leads to a complete and centralized view that maximizes network stability and security.
The Importance of a Vendor-Agnostic NAC
When selecting network access control, consider an agnostic solution. This ensures reliable monitoring even when a wide variety of network components are used. Variability can occur as the result of a merger, acquisition or internal network expansion that unintentionally led to mismatched components. A vendor-agnostic solution makes deployment much easier and gives you confidence that the security solution will work with existing systems.To fully manage today’s demanding networks, a network access control solution must also support every type of authentication technology, which checks to see if a user’s credentials algin with the credentials of an authorized user.
Not all vendors provide this capability or allow it to work with other technologies, such as 802.1X and SNMP. With a scalable NAC solution, existing infrastructure can be used. When a change occurs, the rules, automations and processes in the background ensure that no additional measures are required without manual intervention by the IT administrator. This provides an advantage in the public authority environment, for example, when administrative districts and organizational structures change after a legislative period.
Network Access Control Supports New Ways of Working
The pandemic has brought on mobile and hybrid work environments that require virtual collaboration. Pragmatic solutions must maintain employees’ ability to work and communicate effectively while ensuring confidentiality, availability and integrity.Despite the daily news about cyberattacks and newspaper reports about hacked companies facing ransom demands, many companies still struggle to secure network endpoints. According to a new ThoughtLab report, the average number of reported cyberattacks and breaches rose sharply by 15.1% last year as compared to 2020—while 41% of executives don’t think their security initiatives are keeping up with digital transformation.
A network access control solution helps you close this gap by making it simple to add new authorized devices to the network. When they’re added to a list of trusted devices, the devices can be seamlessly integrated into the existing company workflow.
Controlling network access requires intelligent handling of BYOD devices and company-issued devices.
Company-owned devices can easily be recognized on the network by connecting a mobile device management system as an identity source to an NAC solution. From there, the device can be authorized for the defined network area.
BYOD devices are trickier. Authorized employees can connect their personal devices to the network access control solution’s guest portal. By entering their usual Windows username and password, they’re given the opportunity to register the device and operate it within the company network based on a policy. Once the defined terms of use for operation are accepted, the user can connect the device to the network with one click.
After registering, the network access control solution’s guest portal grants access only when the access data is valid. If an employee leaves the company, then his or her personal endpoints will no longer be granted access to the corporate network.
Act Now to Prioritize Network Security
Implementing a flexible, scalable and efficient network access control solution adds significant value to your network security approach. It increases network visibility, reduces cyber threats and improves network performance.
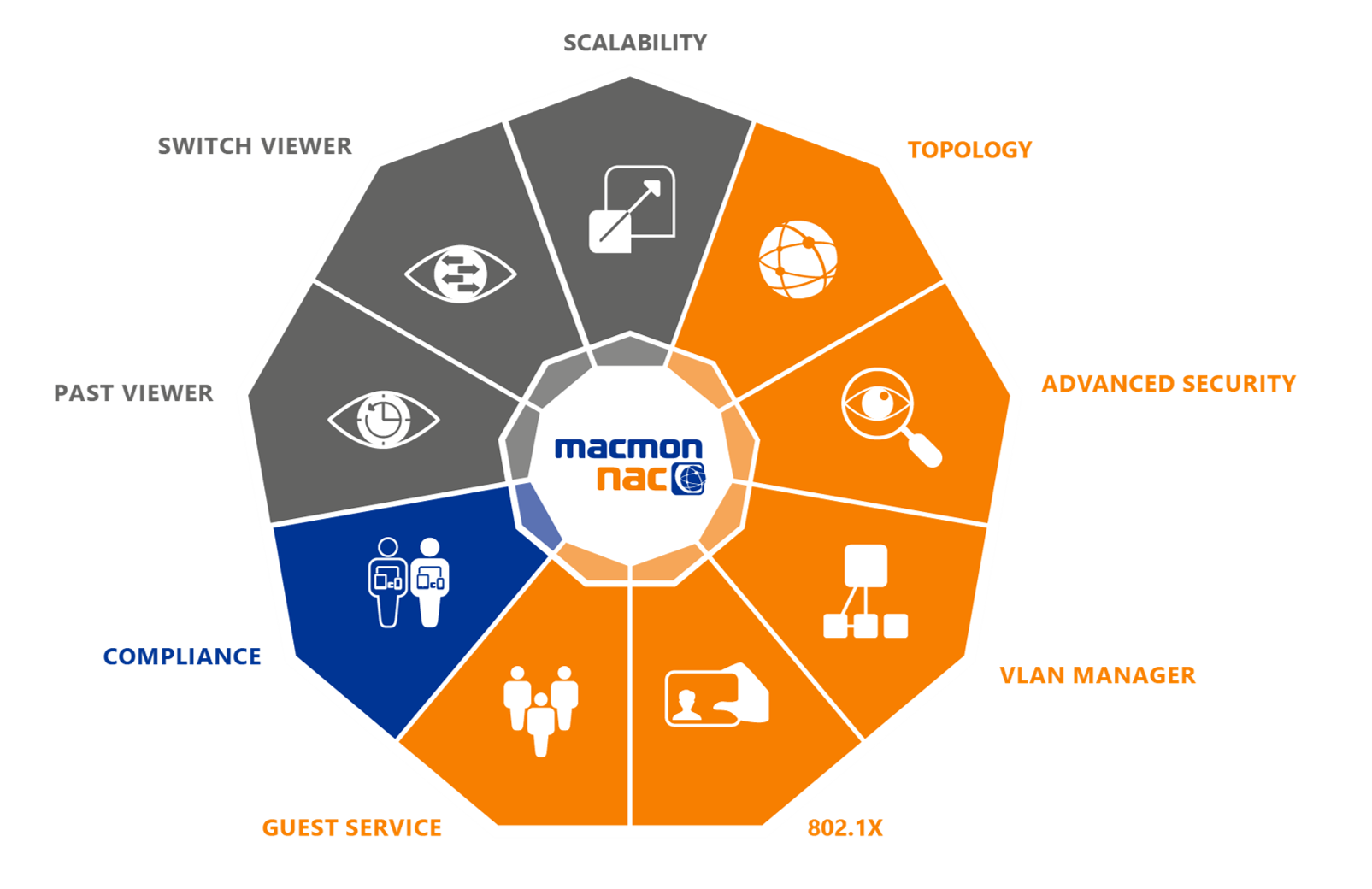
Learn more about macmon’s Network Access Control solution.