Three Ways to Improve Your IP Network Security
Improving upon your IP network security is vitally important, especially considering that many of today's industrial networks use Ethernet alongside legacy protocols that were designed long before security was a main goal, such as with TCP/IP protocols. However, this doesn't mean that improving your network security needs to be complicated.
In this blog, we'll take you through three of the most effective ways to notably improve your IP network security. At a high level, there are:
- Implement a "zones and conduits" network architecture for new networks or major upgrades.
- Move services used by many devices to demilitarized zones (DMZs).
- Ensure your network is using the most current IP standards and best practices.
1: Taking a Zones and Conduits Approach
In today's networks, security can be created through a combination of different, independent security layers. This is so that anyone attempting to compromise or attack a network must overcome several different security mechanisms to achieve their goal, making a breach less likely to occur. It's also a precautionary redundancy measure that prevents the network from becoming compromised if one layer becomes flawed or ineffective.
A recent example of the benefits of using several security layers are the attacks against the WPA2 handshake. While the KRACK attack weakens WLAN security, networks and systems that use additional security mechanisms – like TLS or a strong segmentation of the WLAN network and the wired networks – are less at risk than networks that solely rely on a single mechanism.
The separation of the network into segments or "zones" allows those in charge of network security to track and monitor traffic between different areas of the network. Filtering rules can then be set to only allow traffic that meets certain conditions to pass from zone to zone. In the diagram below, you can see a red and white barrier between each zone in the network. This represents the conduit that exists between zones. When a breach is detected in one zone, these conduits close off the attacker to all other zones.
This practice should be taken into consideration when constructing new networks, as well as when updating existing networks within currently operating facilities.
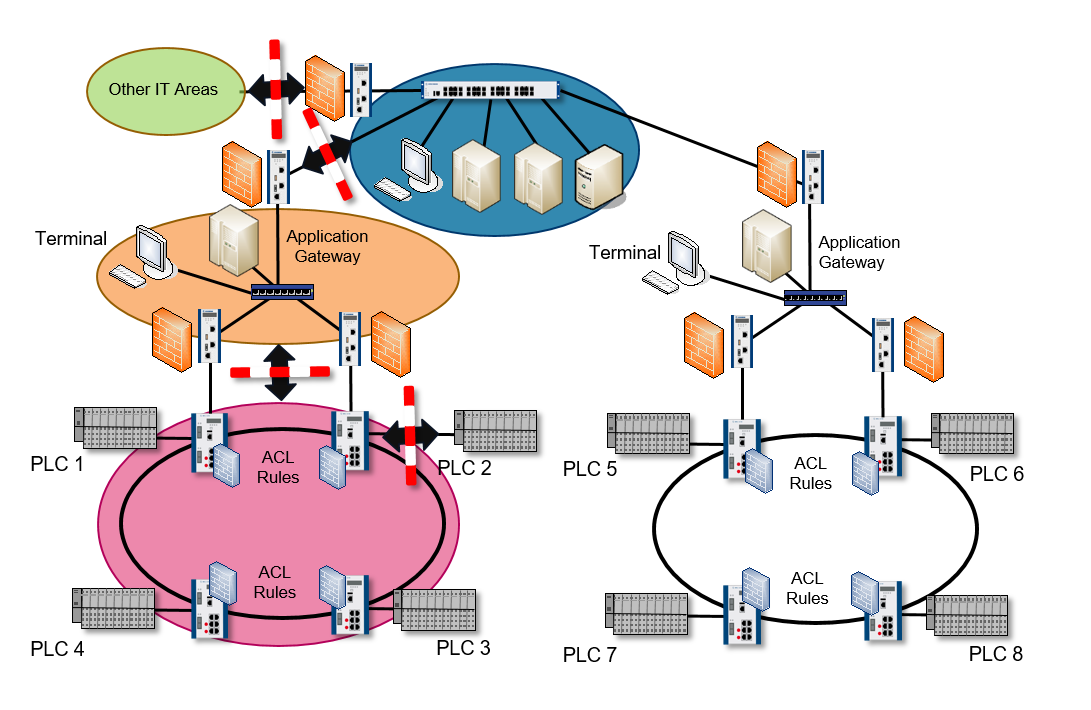
Figure 1: A diagram of how zoning is achieved within a network. Each colored area represents a segmented zone within the network, with each of the zones being connected via a conduit that monitors and regulates traffic between zones.
2: Moving Devices to a DMZ
A demilitarized zone (DMZ) functions as an isolated network that spans the gap between your private network and a larger connected network, such as the internet. DMZ networks are given this name because of the way in which they function much like the military definition of a DMZ. These areas belong to neither of the areas it borders. DMZs within an IP network are therefore neither as secure as the internal network, nor as insecure as the public internet since they can be tightly restricted and monitored. Hence, DMZ-type zones act as a neutral middle ground for information to pass through.
This type of segmentation is of utmost importance for companies that are required to open their network to larger and more insecure outside networks (e.g., the internet). This is because these companies often provide services to users outside of their local area network, such as DNS server, email and web access – services that subsequently and inherently allow a 24/7 link between their networks and potential outside attacks.
When these host services are placed into a subnetwork, like a DMZ, the greater network is protected from attacks or security breaches should one of the services in the DMZ become compromised. Firewalls are also put in place between the DMZ and the external internet, as well as between the DMZ and the internal network. These firewalls restrict the access that host services have to both external and internal networks. Access to the external internet is restricted in order to make the DMZ more secure than the external network, and DMZ access to the internal network is restricted in order to maintain the highest level of internal network security.
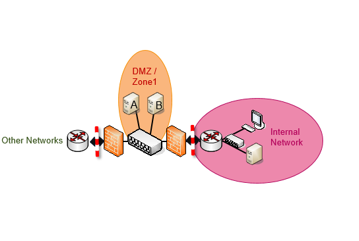
Figure 2: A diagram of how DMZs are configured. The "internal network" is connected to the "other networks" (commonly the internet) via the neutral DMZ sub-network.
3: Tapping Best Practices for Ethernet Security
Understanding current and future best practices in the security space should always be on your team's radar. By leveraging what other experts have seen work, you can move more quickly and easily to add security that is tried and true.
CURRENT: Ways to Improve Your Security Right Now
If you're looking to take immediate action, here are some of the ways in which you can notably improve the security of your Ethernet networks right now:
- Start with Physical Security – Use locked cabinets to house your network devices. Also consider making your switches and routers physically inaccessible. Because this practice doesn't involve the actual components of the network, it can often be overlooked as a security measure, but is no less important in creating a well-protected network!
- Port Configuration – Disable unused ports via switch management and configure ports to only permit traffic to/from specific IP or MAC addresses. Using features such as port security, dynamic ARP Inspection, IP source guard and DHCP snooping can support such limitations. If a different IP or MAC address is discovered on a switch port, the port will be taken down and no longer open to spoofing attacks.
- Authentication – Use certificate or credential-based authentication to ensure unique access credentials for every device.
FUTURE: A Top Consideration for Improving Security Going Forward
Besides implementing proper network segmentation, we suggest that these network security improvements be on the horizon for your industrial network:
- Always keep your devices' software and firmware up-to-date – The recent KRACK attacks against the WPA2 WLAN handshake show that even widely used and rigorously analyzed protocols are susceptible to attack. While these new attacks seem devastating at a first glance, future attacks can be easily stopped by fixing the underlying software flaws. Like other quality vendors, Belden has reacted quickly to promptly provide software updates for its industrial wireless devices. Regularly updating network devices' and end-systems' software is a basis for thwarting such threats. Introducing a patch management process that checks whether all devices in a plant run the most recent and most secure software is essential for maintaining a high security in wired and wireless networks today.
- Increase wireless protection with Protected Management Frames – The current IEEE 802.11i standard for wireless communications uses Advanced Encryption Standard to encrypt your private data so that attackers cannot decrypt it and steal your private data. An attacker's next course of action would be to resort to a denial-of-service (DoS) attack to slow down or limit your access to the wireless network. The 802.11w standard, known as Protected Management Frames (PMF), shields the legitimate client by introducing encryption and integrity protection for management frames. These management frames are used to control the behavior of the devices in the network and can be misused to trick wireless devices into voluntarily disconnecting from the network. This attack vector can be thwarted if encryption and integrity protection are enforced for these important frames. Moreover, protecting these frames makes attacks that use forged management frames as a first attack step more complicated. WPA2 brute force attacks and the newly discovered KRACK key reinstallation attack use forged management frames to conveniently disconnect clients from the network. While PMF cannot completely prevent such attacks, it still makes executing them less easy.
